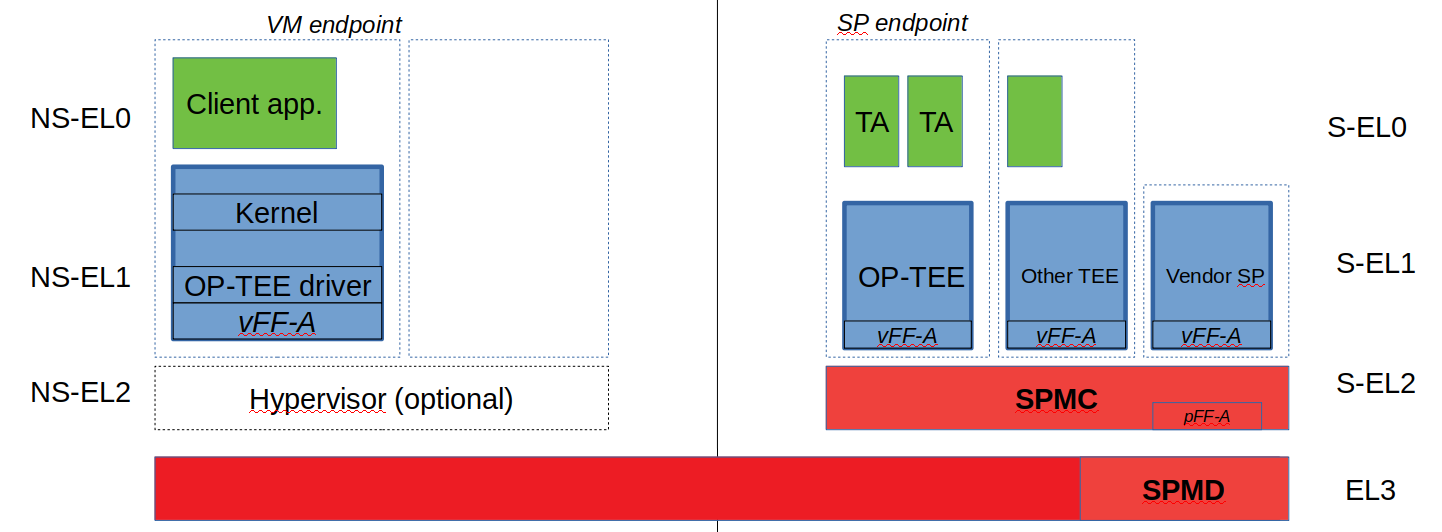
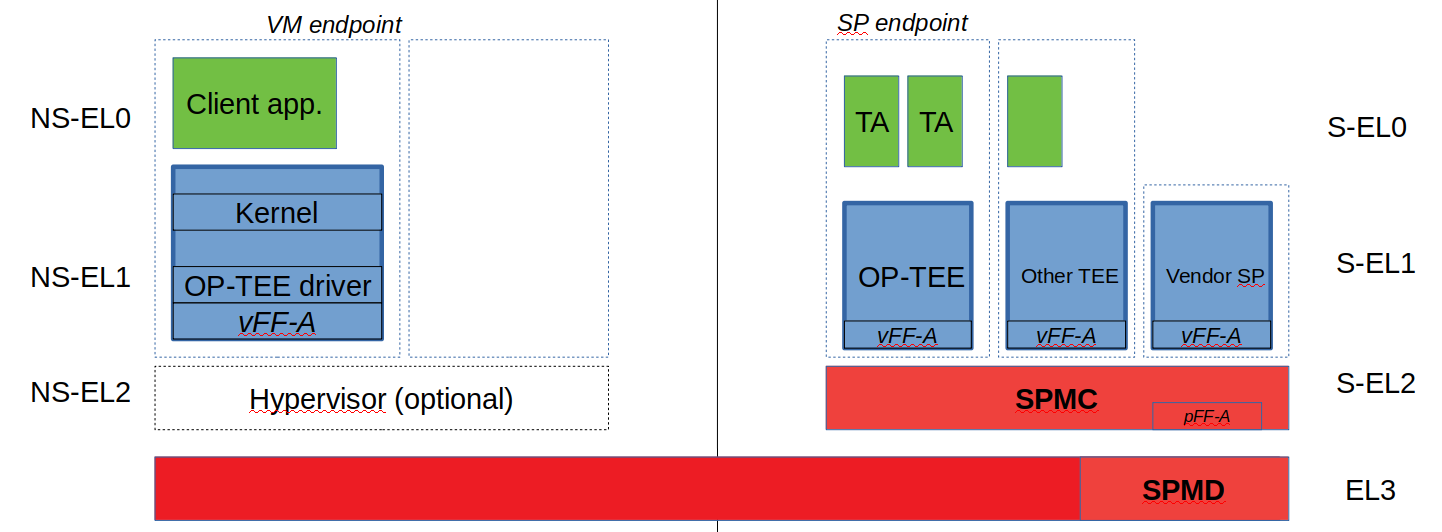
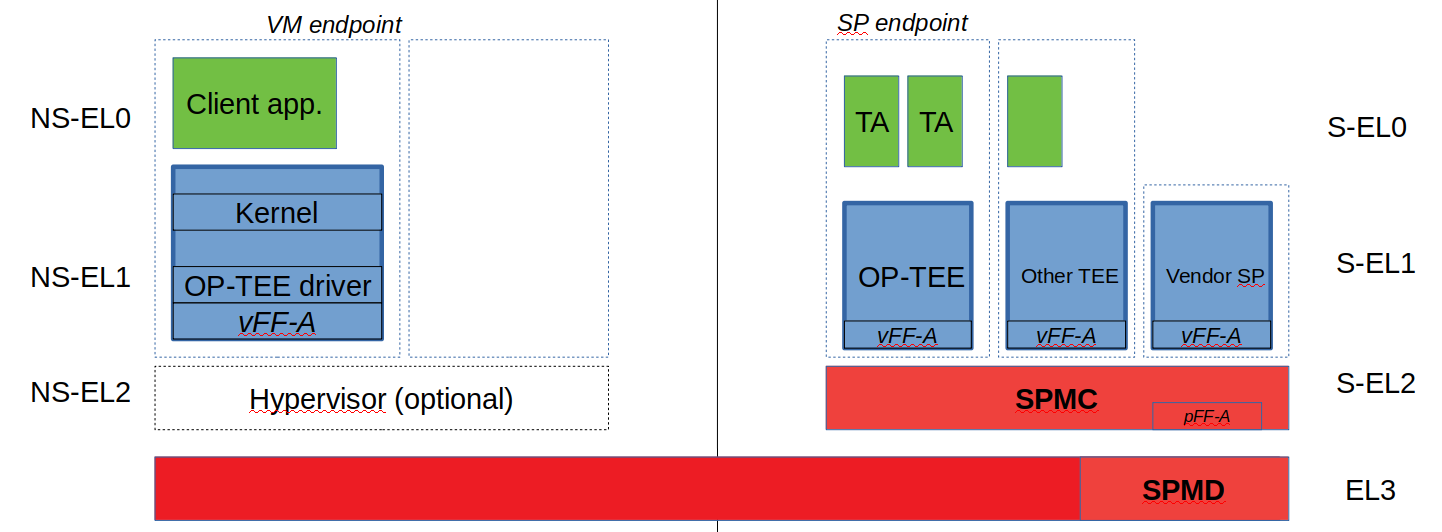
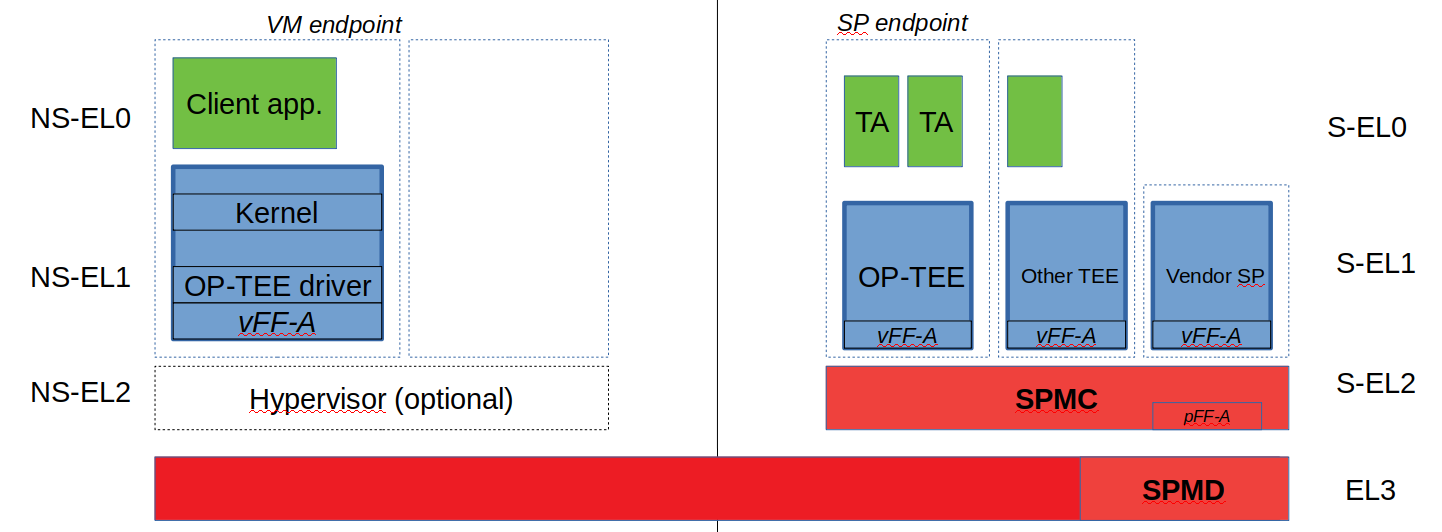
docs: spm design document refresh
General refresh of the SPM document.
Change-Id: I2f8e37c3f34bc8511b115f00b9a53b6a6ff41bea
Signed-off-by:  Olivier Deprez <olivier.deprez@arm.com>
Olivier Deprez <olivier.deprez@arm.com>
| W: | H:
| W: | H:
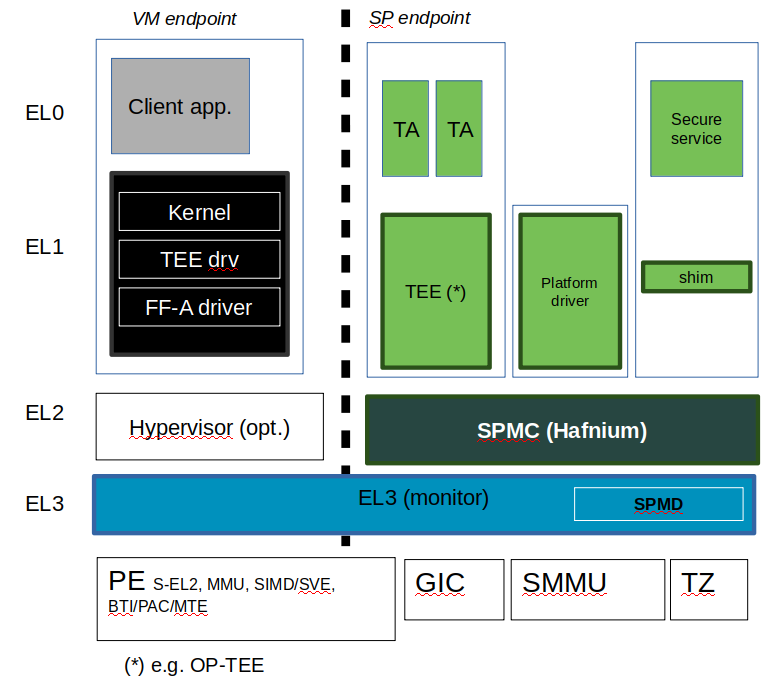
84.2 KB
General refresh of the SPM document.
Change-Id: I2f8e37c3f34bc8511b115f00b9a53b6a6ff41bea
Signed-off-by:  Olivier Deprez <olivier.deprez@arm.com>
Olivier Deprez <olivier.deprez@arm.com>
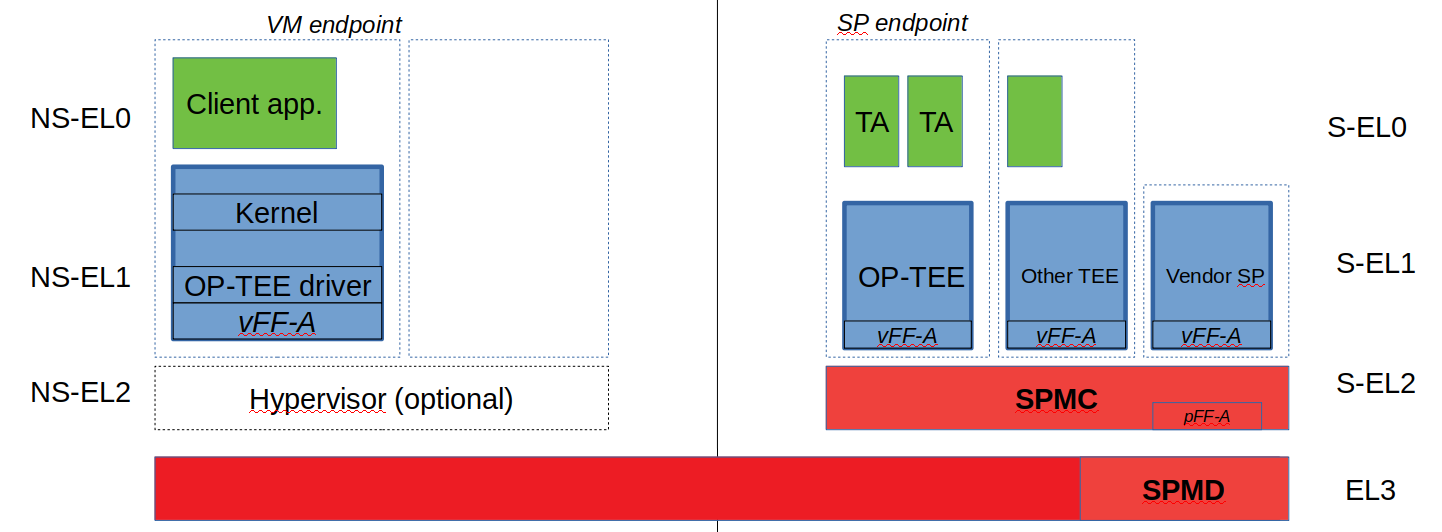
81.4 KB | W: | H:
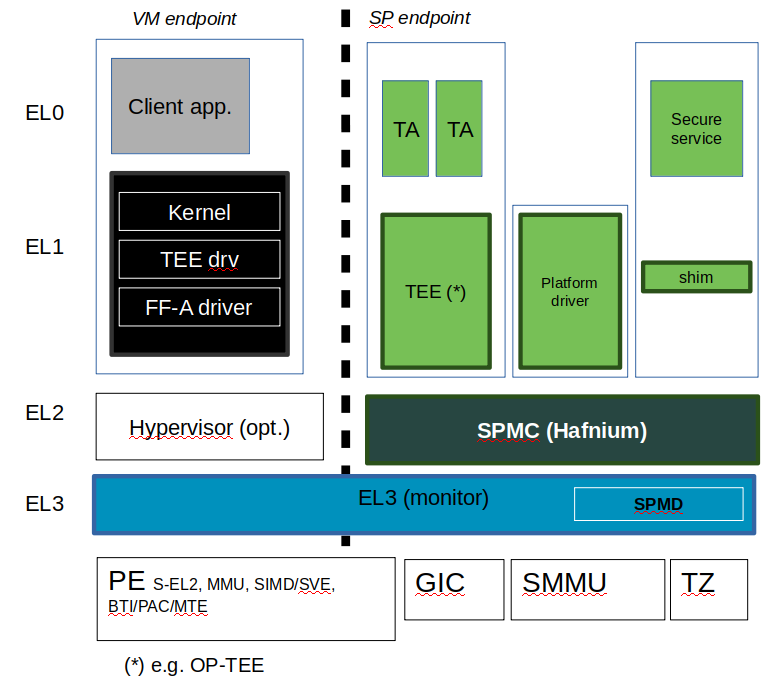
52.1 KB | W: | H:
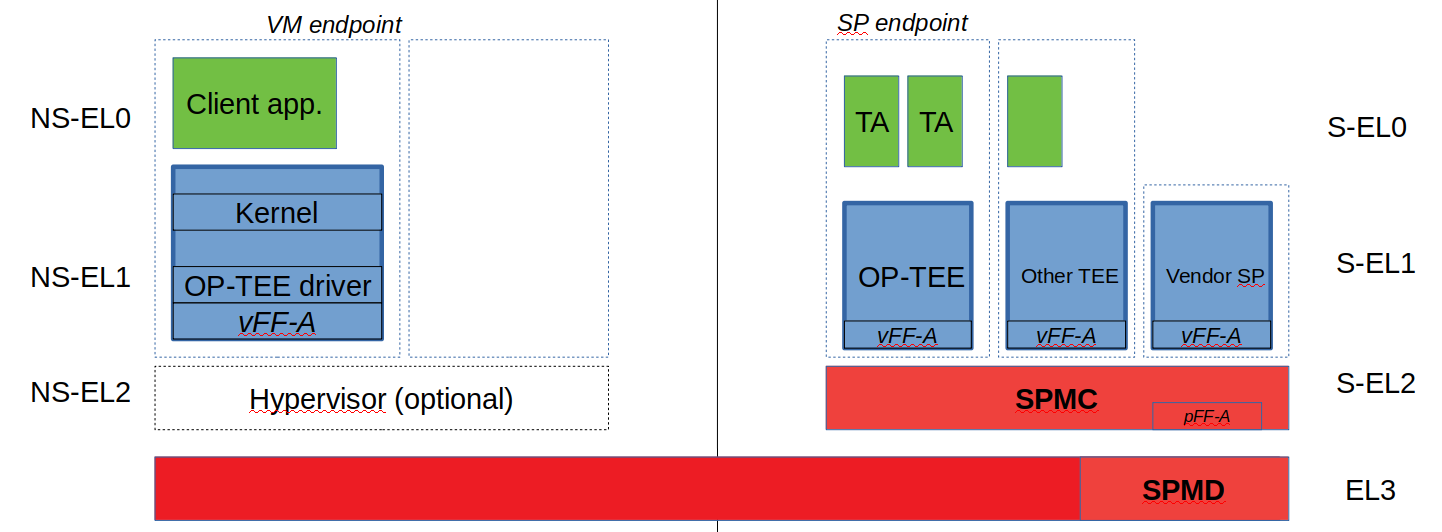
84.2 KB